How to measure the dollar value and ROI of cyber security
With the rise of cyber attacks and the myriad of cyber products on the market, it can be difficult to know which cyber security initiatives to focus on to get the best value in terms of spend and effectiveness.Key Takeaways
- While many organisations see cyber security as a cost centre, it should be framed as an investment in protecting business-critical assets.
- Framing cyber security in terms of avoided costs, improved confidence and reduced regulatory intervention makes its ROI more tangible for executives and boards.
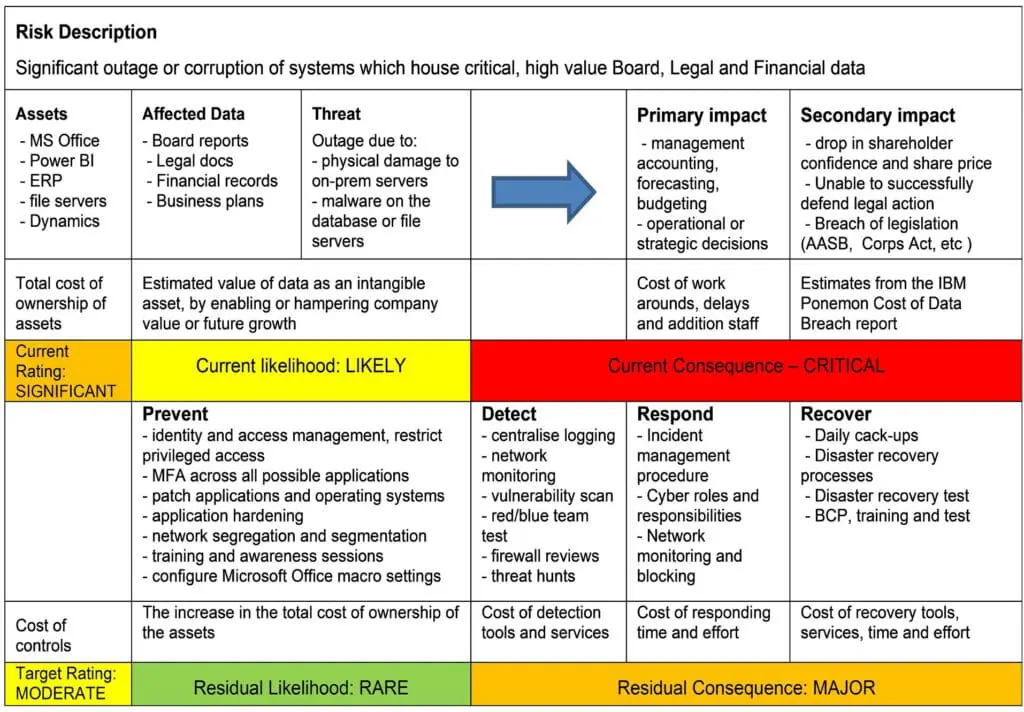
- Using structured models like risk scenarios mapped to controls helps organisations translate security outcomes into dollar values and justify spending decisions.